TRANSITION TO PERSONAL IDENTITY VERIFICATION (PIV) AUTHENTICATION CERTIFICATE INFORMATION PAGE |
|||
|
NOTICE:
Big changes are coming to the way you access your Enterprise Email, PLEASE read, understand, and SHARE this page with all you know who access DoD Enterprise Email (https://web.mail.mil)
Between 14 October 2019 and 10 February 2020 ALL Army personnel will have their Enterprise Email converted to use the Authentication certificate and no longer use the Email certificate when accessing DoD Enterprise Email (DEE), DoD Enterprise Portal Service (DEPS) (SharePoint), Defense Collaboration Service (DCS) (online meetings).
ARCyber Situational Awareness Report 2019-157 can be viewed here on AKO 2.0 (CAC required link)
All Army personnel must have the Authentication certificate on their CAC.
All CACs issued since the end of February 2018 have the Authentication certificate already activated. If your CAC was issued prior to the end of February 2018, please follow these links to activate your Authentication certificate on your CAC. Follow these instructional links 64bit / 32bit Windows computers for specifics.
Mac users who upgrade to Mac OS Catalina (10.15) need to select the certificate WITHOUT the word Email in it once migrated. Please visit https://militarycac.com/catalina.htm for the most up to date information on Apple's newest version of Mac OS.
Signing Adobe PDF forms might work in Mac OS Catalina. Find out specifics here
Schedule for Army personnel migration. If you are unsure which Command (left column) you fall under, call the Army Enterprise Service Desk-Worldwide at 866-335-2769 and ask.
Click on image below for a larger version
Users should receive up to three notices for their pending transition
Date the PIV template is processed One week prior to the transition date Day before the transition date
This notification is in three parts
Part 1 – General Effective Tuesday <pick date above> your Enterprise Application Common Access Card (CAC) authentication will transition from Email certificate to Authentication certificate. The following DISA hosted websites are affected by this transition: DOD Enterprise Email (DEE), UEM Mobility, DOD Enterprise Portal Service (DEPS), Defense Collaboration Service (DCS), and milDrive.
**It is recommended that you copy and save this email and the documents at the below links prior to your date of transition so that you have it for reference after your account has been transitioned.**
Part 2 – Activate your PIV Auth Certificate. If you have not already done so, activate your PIV certificate at the RAPIDS Self-Service CAC Maintenance website. Consult 64bit / 32bit links for specific instructions. If you do not activate your PIV certificate you will not be able to use Enterprise applications listed in Part 1.
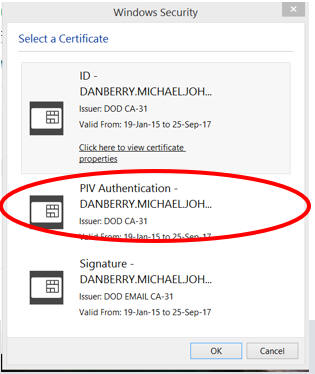
Part 3 – Once your account is transitioned you must begin using your Authentication certificate. When you launch Enterprise applications, you have to select other certificate and choose your Authentication certificate (16 digits) to get access. If you are interested in what the 16 digits mean, look at: https://militarycac.com/EEmail.htm#Information_30a::
If you have any issues please contact AESD-W at 866-335-2769 or your local service desk for assistance.
DMUC iOS users may experience slight email delays and minor
setting resets during PIV account migration. iOS users currently
using iOS "Purebred Email" will need to simply update to Email+.
If you are impacted, refer to the DMUC PIV-Auth
User iOS Email Troubleshooting QRG
https://disa.deps.mil/ext/cop/dod_mobility/metrics/Tier%201%20Library/DISA%20Tasking%20Orderings%20(DTO)/End%20Users/PIV-Auth%20DMUC%20User%20iOS%20Email%20Troubleshooting%20QRG%20(U).pdf
|
|||
If you have questions or suggestions for this site, contact Michael J. Danberry
. Last Update or Review: Sunday, 03 April 2022 19:43 hrs
The following domain
names all resolve to the same website: ChiefsCACSite.com,
CommonAccessCard.us, CommonAccessCard.info, & ChiefGeek.us
|